Contents: Overview
VMware NSX provides SSL VPN capability through an NSX Edge Services Gateway which they call the SSL VPN-Plus capability. Figuring out how to install SSL VPN-Plus on VMware NSX is not as straightforward as it could be. The SSL VPN client is lightweight and easy to use but the initial setup on the server side can be a little daunting so this is a step by step guide to install SSL VPN with VMware NSX 6.1.2 which will hopefully make it easier.
Pre-requisites before you can begin:
- NSX Manager 6.1.2 installed and configured
- vCenter Server online and functional
- Public facing IP address to assign the NSX Edge (this can be NAT'd, DMZ, public network or firewalled off)
- Enough capacity to deploy an NSX Edge VM in the vSphere Datacenter the NSX Manager and vCenter Server manage
- Define a segregated network, called an IP Pool, only accessible from the NSX Edge VM (IE: 172.16.0.0/24 or 10.1.0.0/16)
- Ability to create routing rules for the above segregated network(s)
These instructions are not meant to be exhaustive and may not be appropriate for your environment. Always check with your hardware and software vendors for the appropriate steps to manage your infrastructure.
There are severe security implications when configuring a VPN service and providing public access to it through the Internet. Verify with the appropriate parties in your organization before performing these steps.
Formatting:
Instructions and information are detailed in black font with no decoration.
Code and shell text are in black font, gray background, and a dashed border.
Input is green.
Literal keys are enclosed in brackets such as [enter], [shift], and [ctrl+c].
Input is green.
Literal keys are enclosed in brackets such as [enter], [shift], and [ctrl+c].
Warnings are in red font.
How to install and configure VMware NSX SSL VPN-Plus
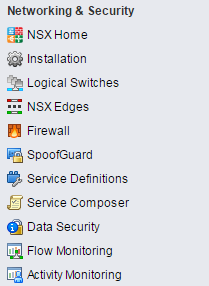
- Log in to your vSphere Web client and select the Networking and Security service.
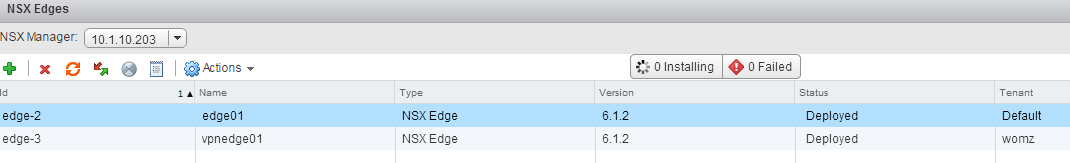
- On the left, select NSX Edges.
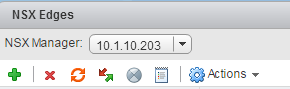
- On the top left, click the green plus button to Add an NSX Edge
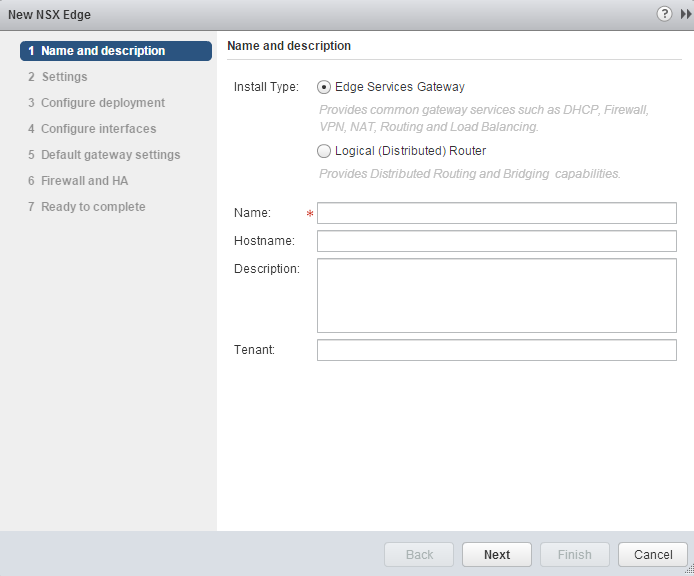
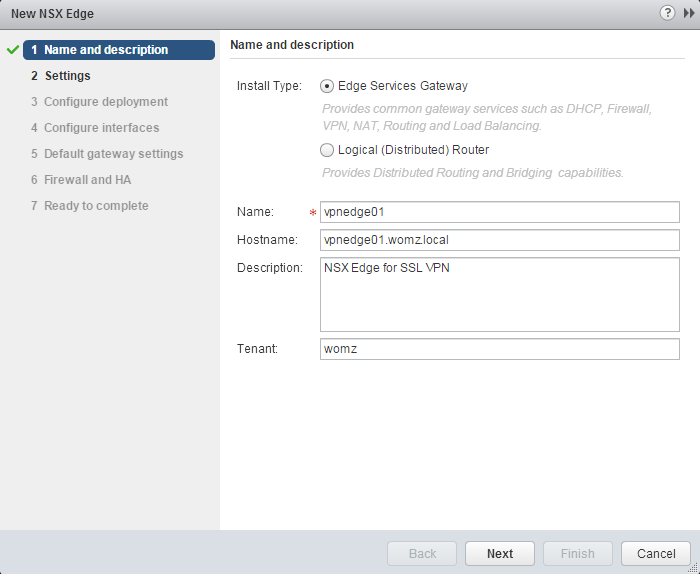
- In the wizard that launches, select "Edge Services Gateway" as the install type. The SSL VPN-Plus service is only available on an Edge Services Gateway.
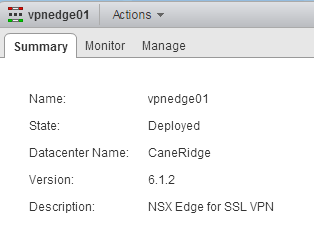
In the name field, this is the display name in the vCenter inventory so it must be unique for the vCenter Server.
In the hostname field, this is the fully qualified domain name of the NSX Edge that will configure itself once deployed. This does not register with DNS or AD, just configures the local hostname inside the NSX Edge OS.
Description can be anything as desired.
Tenant can be used to tag the NSX Edge Services Gateway for a specific customer. - Select Next.
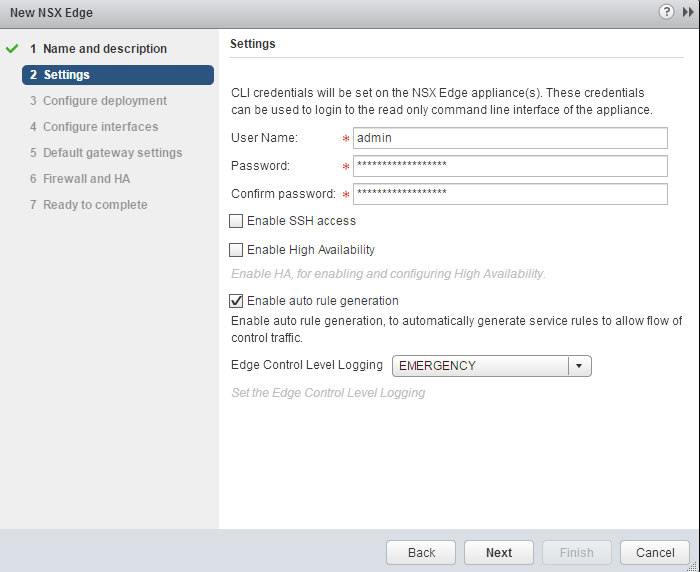
- Type the username for the administrator account used for CLI access, the default is admin.
Type in the password in the next two fields. It must be at least 12 characters, have one upper, one lower, one number and one special character.
If you desire SSH access to the NSX Edge Gateway, check the box for it. The default is unchecked.
Check the box for High Availability if you want to deploy two appliances with the same configuration with one as a warm standby. This is not VMware Fault Tolerance (VMware FT) or vSphere HA. The default is unchecked.
Check the box for Enable auto rule generation to allow NSX to automatically configure firewall, NAT and routing rules for the SSL VPN-Plus services we enable on the NSX Edge appliance. Be aware that this does not generate rules for the segregated network(s), called IP Pools, which will be configured later. - Select Next.
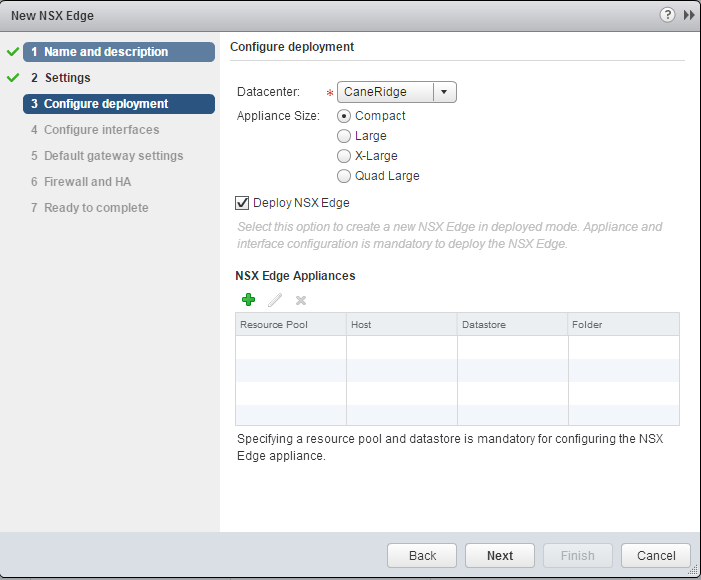
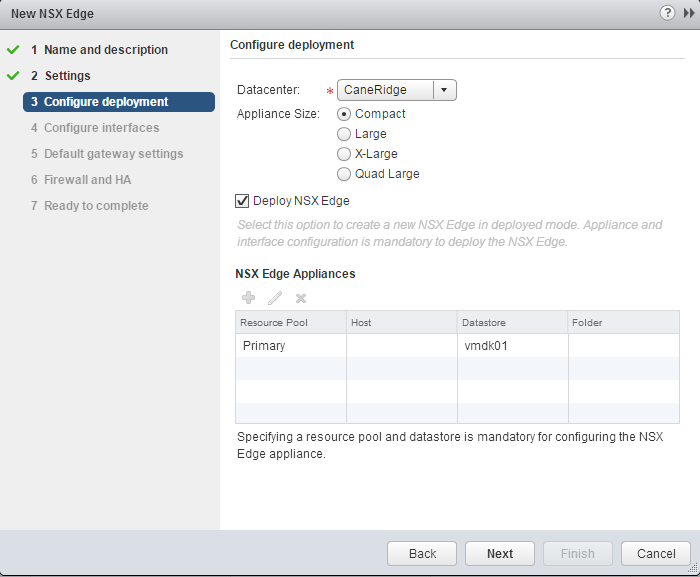
- Select the Datacenter to deploy the VM to.
Select the desired appliance size. (see references for requirements)
Check the box to deploy the NSX Edge after completing the wizard.
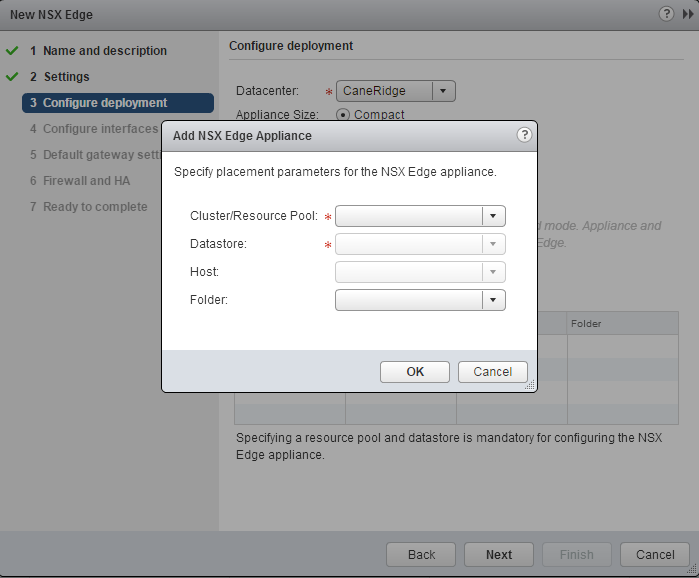
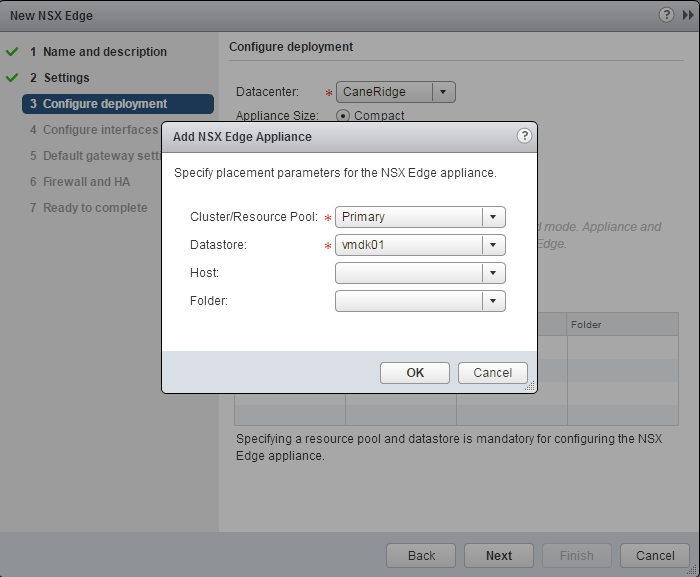
Select the green plus button to define the resource locations. - Select the resource pool, or cluster, to run the compute resources on.
Select the Datastore to put the vdmk and configuration files in.
If desired, select a specific host and folder to put the VM on. - Click OK
- Click Next
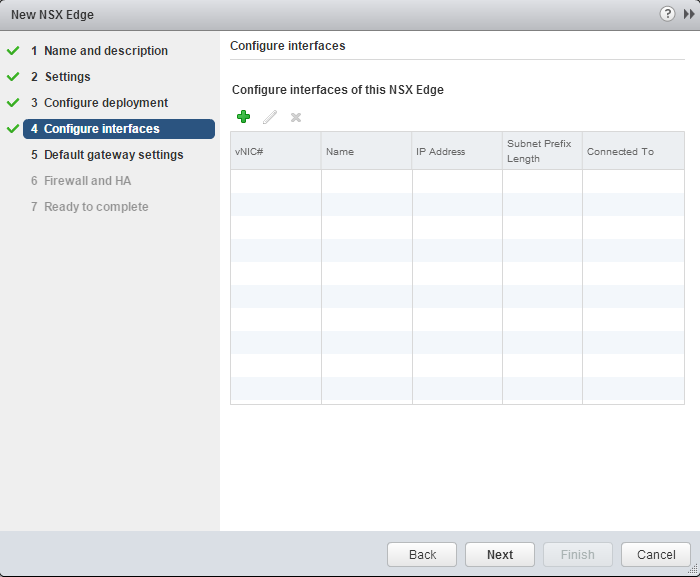
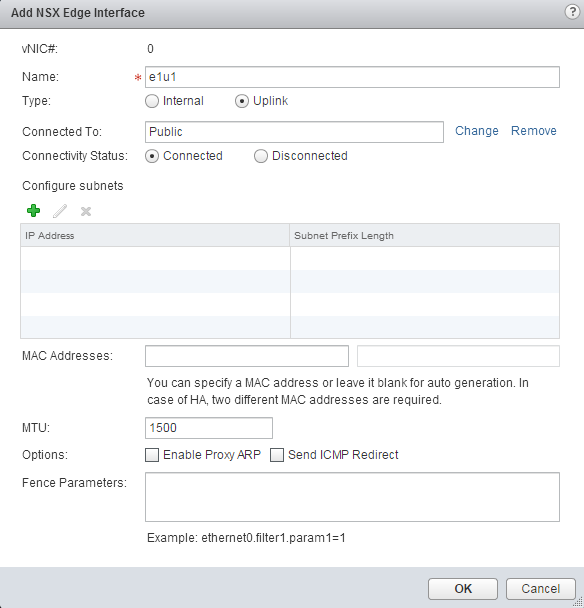
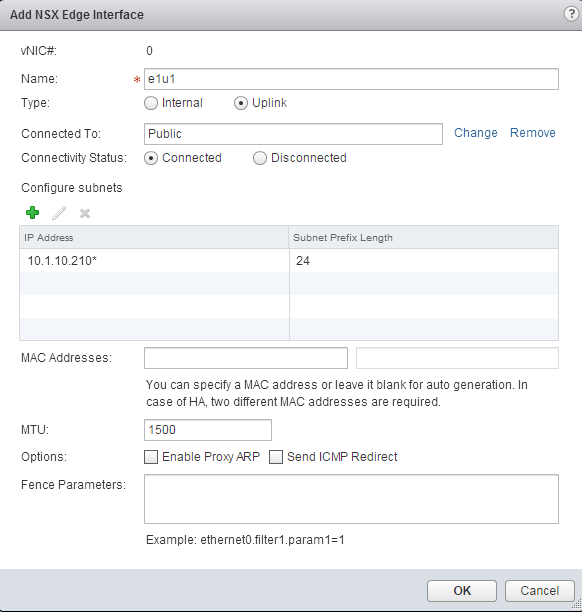
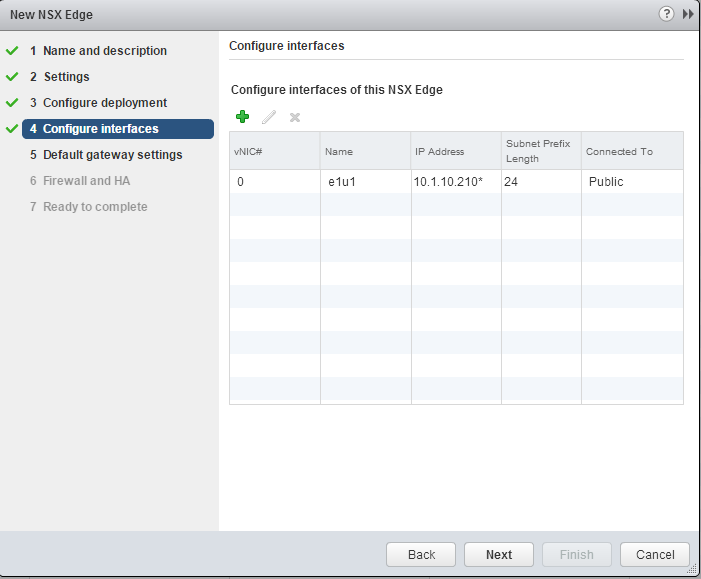
- Select the green plus button to add an interface to the Edge Gateway
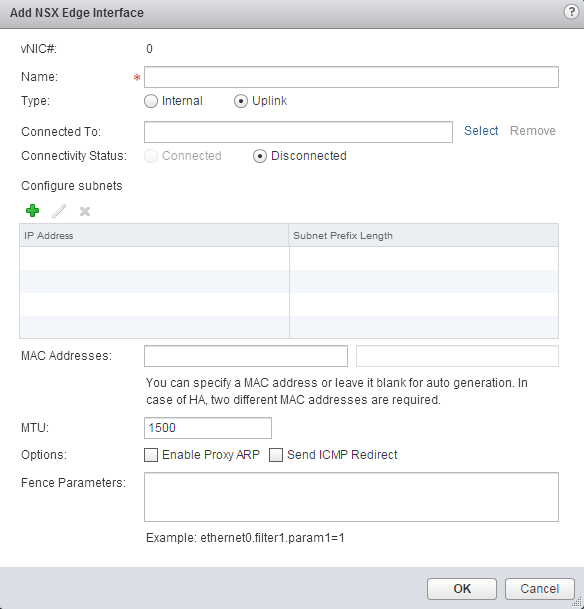
- At least 1 uplink interface is required. Give it a name.
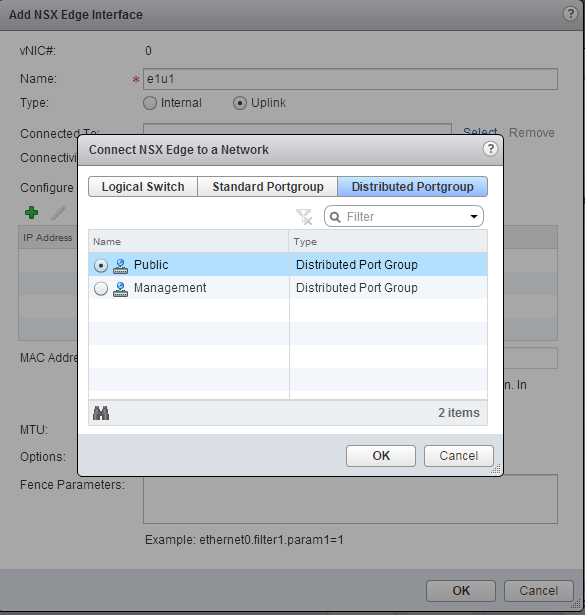
Click the "Select" link to choose the portgroup the VM's uplink interface should be connected to. - Find the portgroup you want to use and select the radio button.
- Click OK
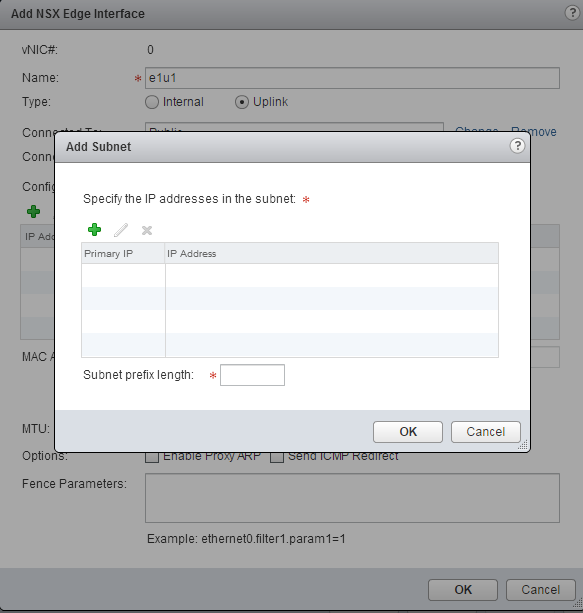
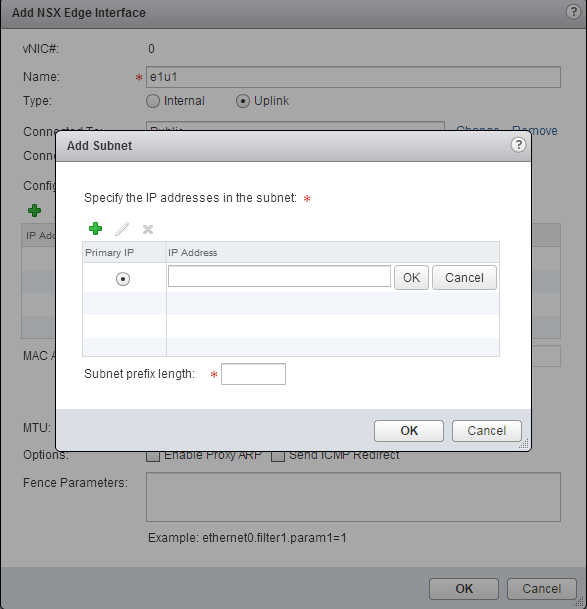
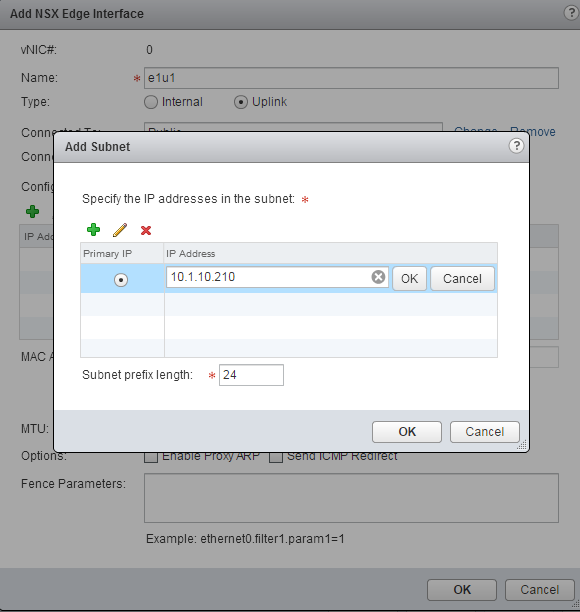
- Click the green plus button to configure the uplink's IP information.
- In the new mini-wizard, click the green plus button to add an IP address.
- Type in the IP for the NSX Edge Gateway to be assigned on its local adapter. If the Edge is being NAT'd then put in the internal IP address. If you are using a DMZ or some other method where the Edge Gateway is directly accessible from the Internet then put in that IP address.
Click the OK button next to the IP.
Put in the number of bits for the subnet mask, (IE Class C or /24 is 24). - Click OK.
- Change any other values as desired then click OK.
- Click Next.
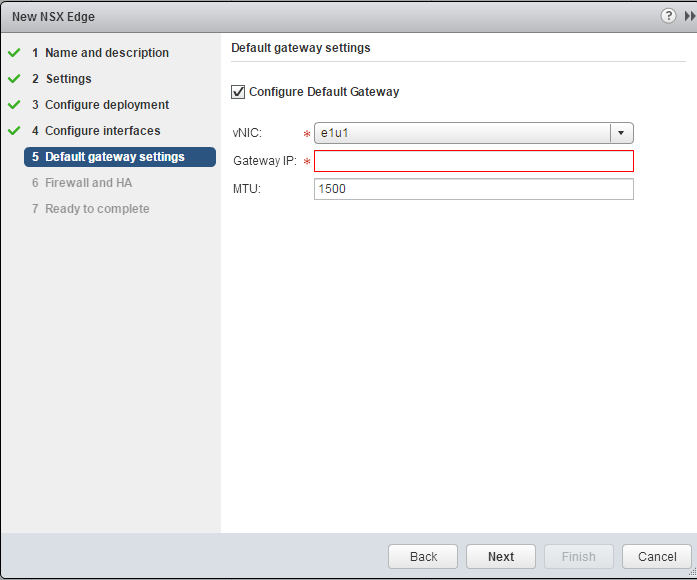
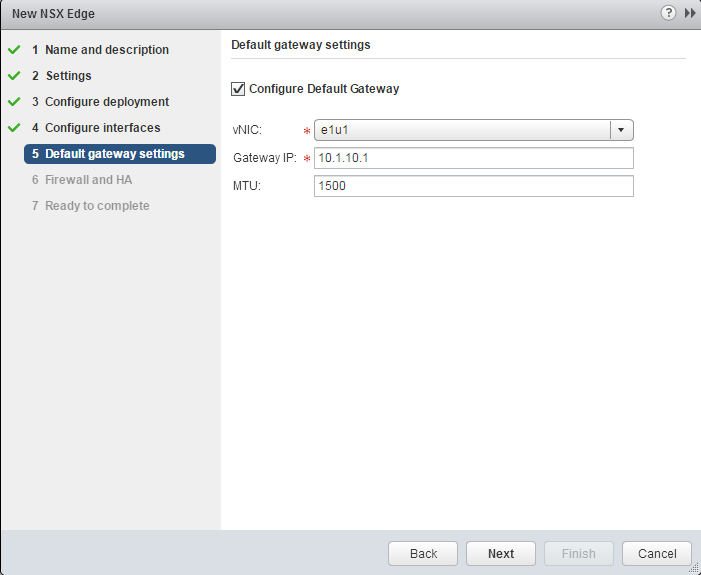
- Type in the default gateway for the IP address you entered above. If you created multiple interfaces be sure to match the interface name to the correct network configuration.
- Click Next.
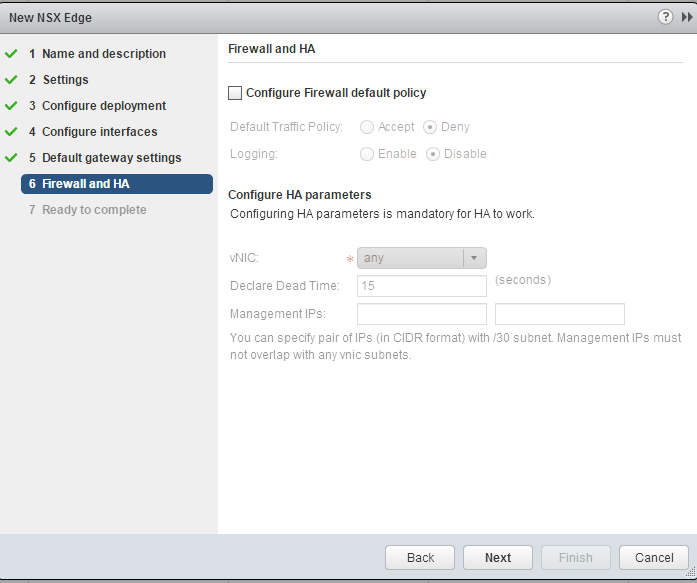
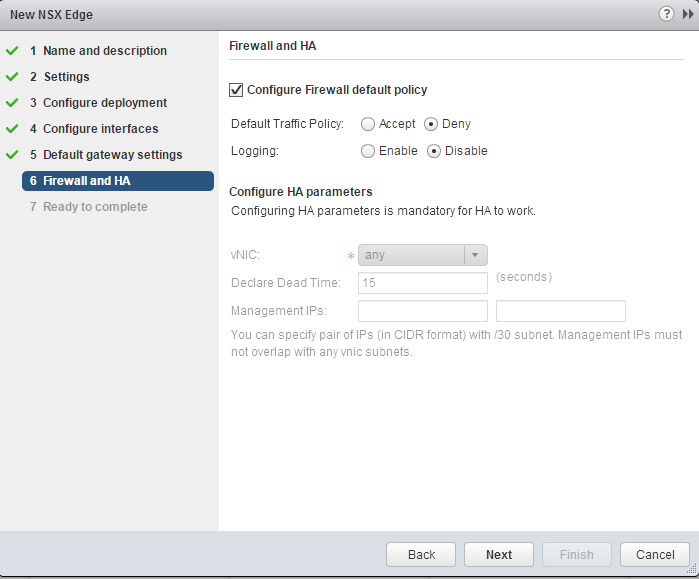
- If desired, check the box to configure the default firewall policy. A good idea is to check this and deny all traffic except for that which is explicitly defined as allowed, which will be done in later steps. You will not lose connection to the NSX Edge, if you checked the box for "Enable Auto rule generation" it will take care of that for you, hence default rules policy.
- Click Next.
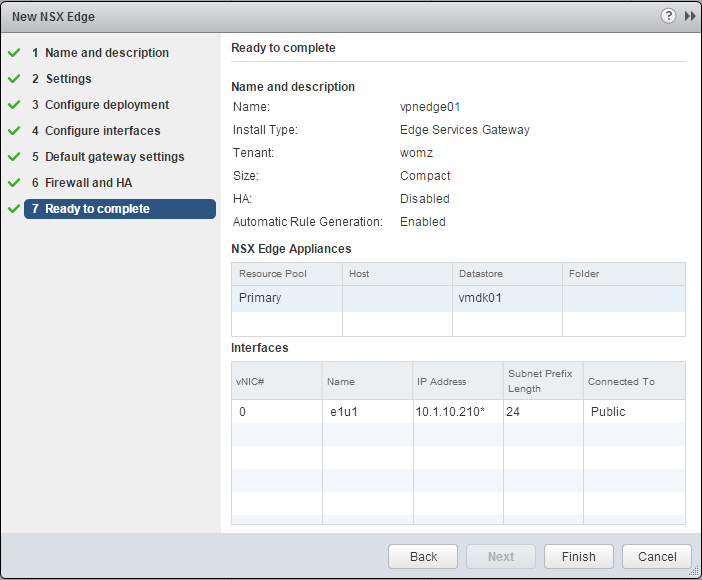
- Verify the settings and click Finish.
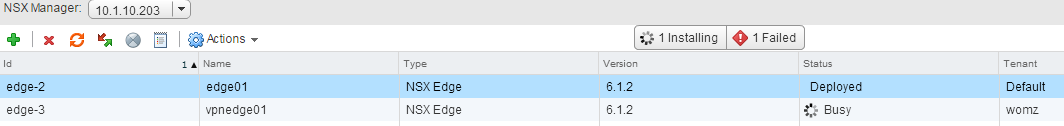
- Wait for the deployment to complete. The status will change from Busy to Deployed when it is ready. In the web client a task does not show up in the recent tasks, though if you open the thick client you will see some operations. If you want to see the details you can view task operations on your specific vcenter, datacenter, or cluster. It took about 3 minutes to deploy in my environment.
- Double-click the NSX Edge you just deployed to manage it.
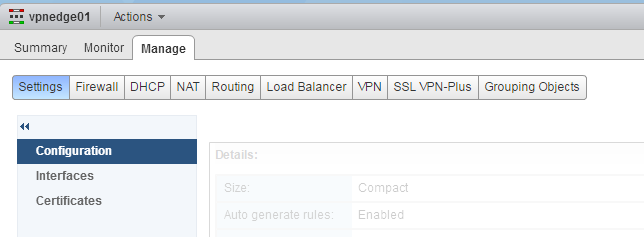
- Select the Manage tab.
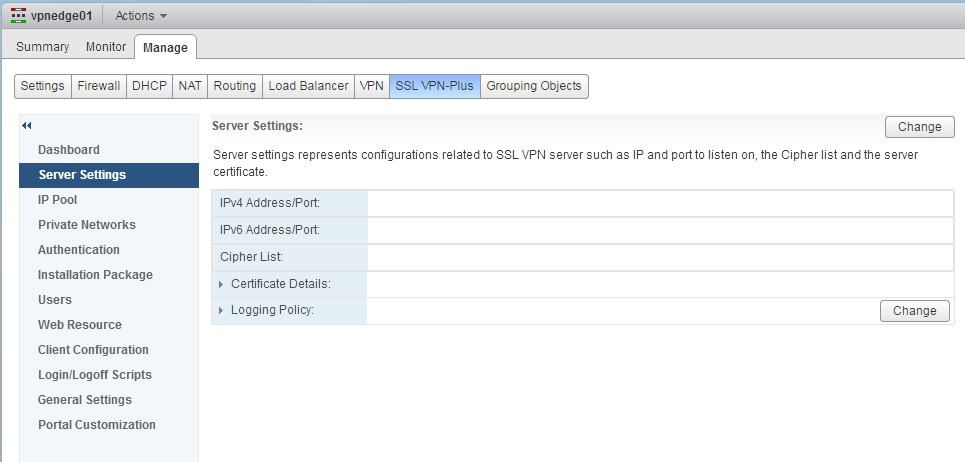
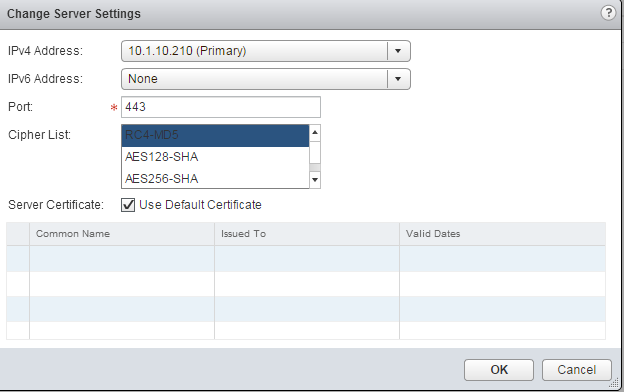
- Select the SSL VPN-Plus tab.
- Select the Server Settings tab.
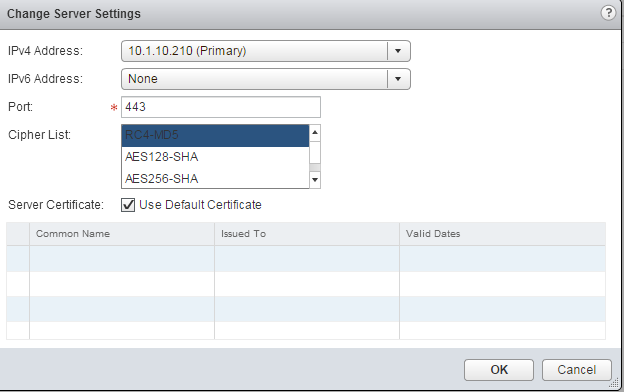
- In the Server Settings area on the top right, click the Change button.
- Select the IP Address you wish to configure the VPN listener on.
Type in the port for the VPN listener to watch.
Change the Cipher List for the SSL connection to use.
Change the Server Certificate as desired. - Click OK.
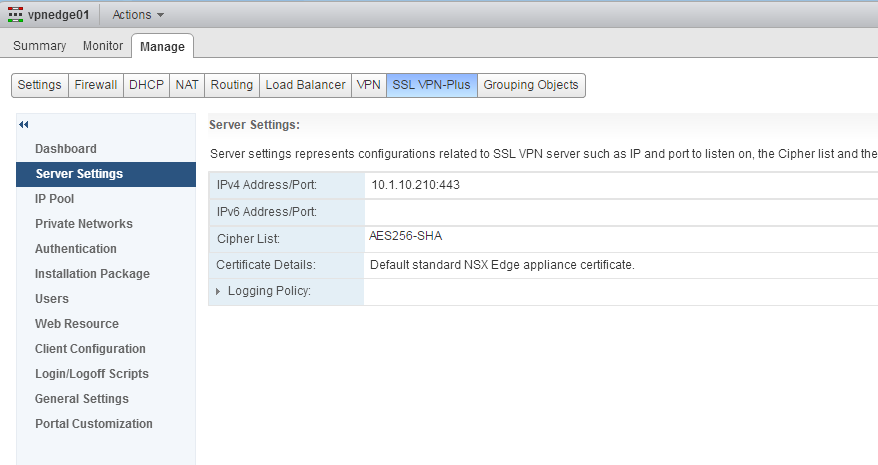
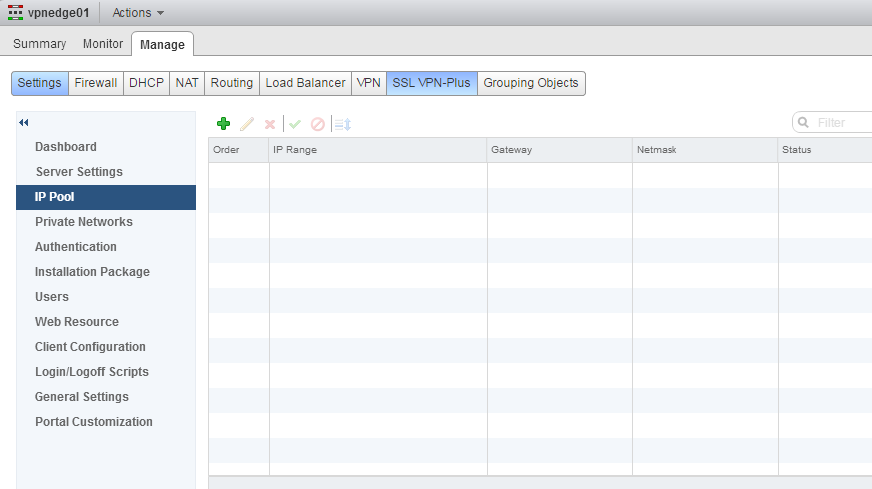
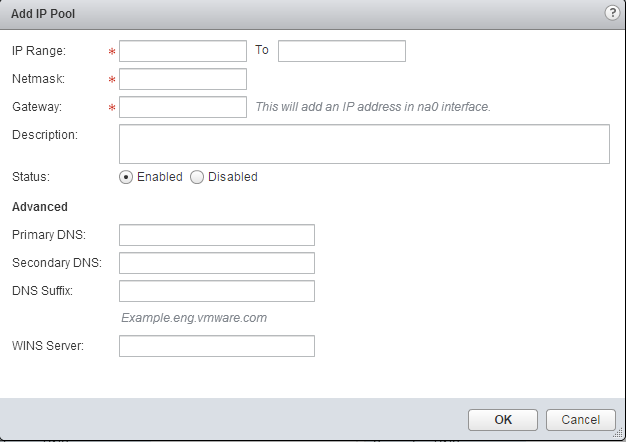
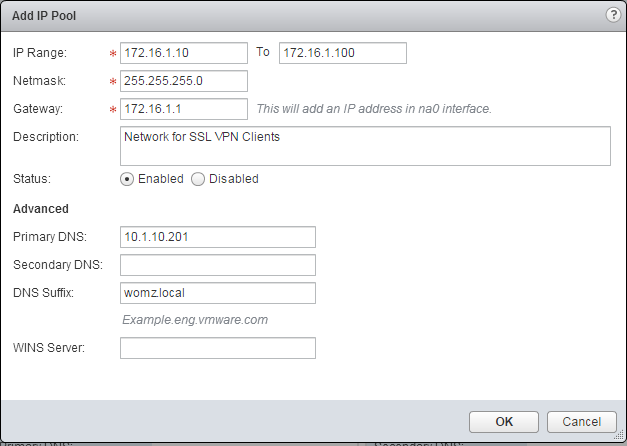
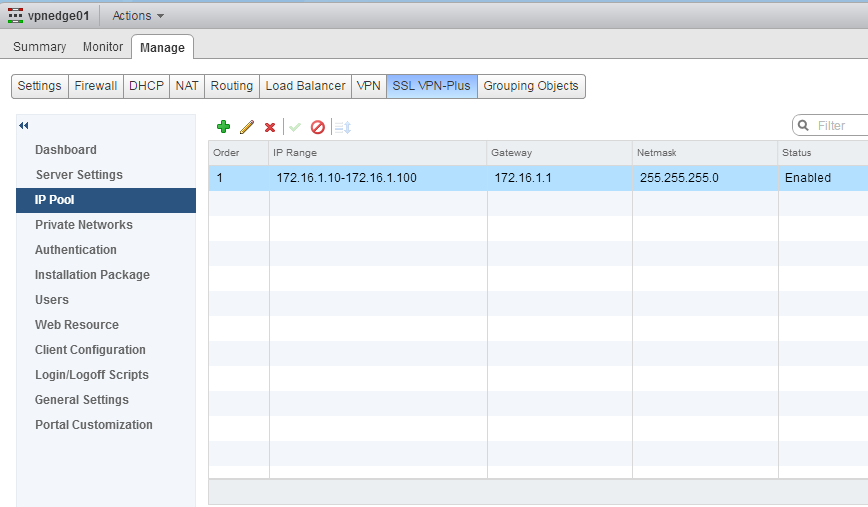
- Select the IP Pool tab.
- Click the green plus button to create an IP Pool.
- An IP Pool is the IP Addresses that the VPN clients will be configured with once they authenticate and connect to your network. This network is segregated from your existing network environment and does not need to be configured on existing network equipment (except for routes).
Type in the start and end range of the IP Pool.
Provide the netmask in dotted decimal (IE 255.255.255.0 for /24 or class C).
Provide the IP you want the NSX Edge to create for itself to use as the gateway for the IP Pool. This IP will be configured on a virtual adapter on the VM.
Provide the primary and secondary DNS servers in dotted decimal format (IE 8.8.8.8).
Provide the DNS suffix for the domain the systems are being hosted on, even if this is not a Windows environment.
Provide the WINS server if needed. - Click OK.
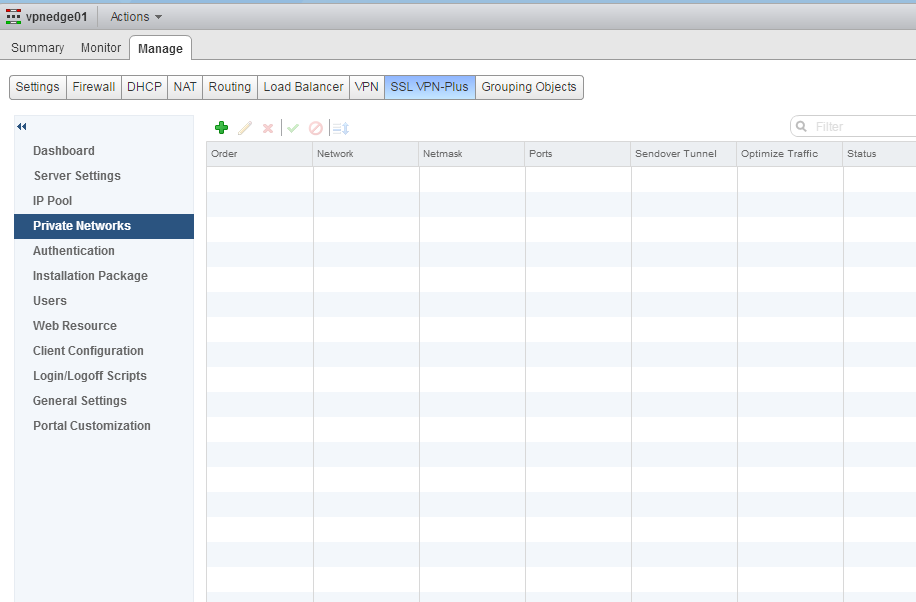
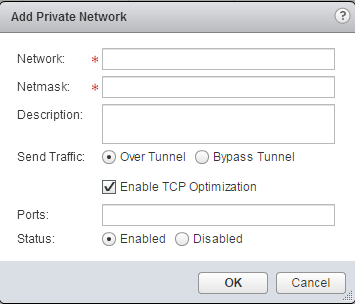
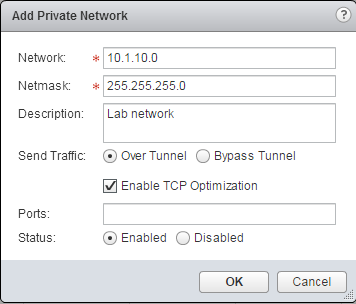
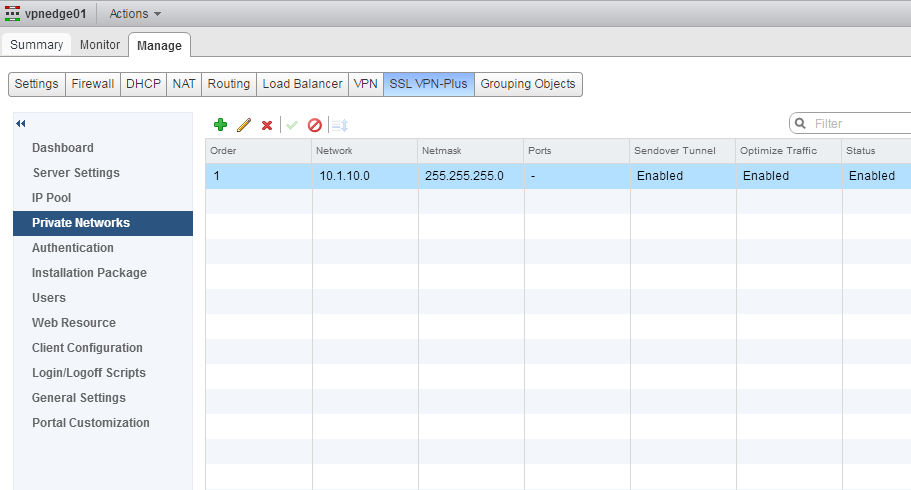
- Select the Private Networks tab.
- Click the green plus button.
- A Private Network is the network(s) you want the VPN clients to have access to. These networks will need to be configured on your existing network infrastructure. In my lab the main network is 10.1.10.0/24 and I want my VPN clients to be able to access it.
Type the network in dotted decimal format.
Type the netmask in dotted decimal format.
Provide a description if desired.
"Specify whether you want to send private network and Internet traffic over the SSL VPN-Plus enabled NSX Edge or directly to the private server by bypassing the NSX Edge."
Select enable TCP optimization.
If you only want VPN clients to be allowed to send traffic into your network over certain ports, define them here. - Click OK.
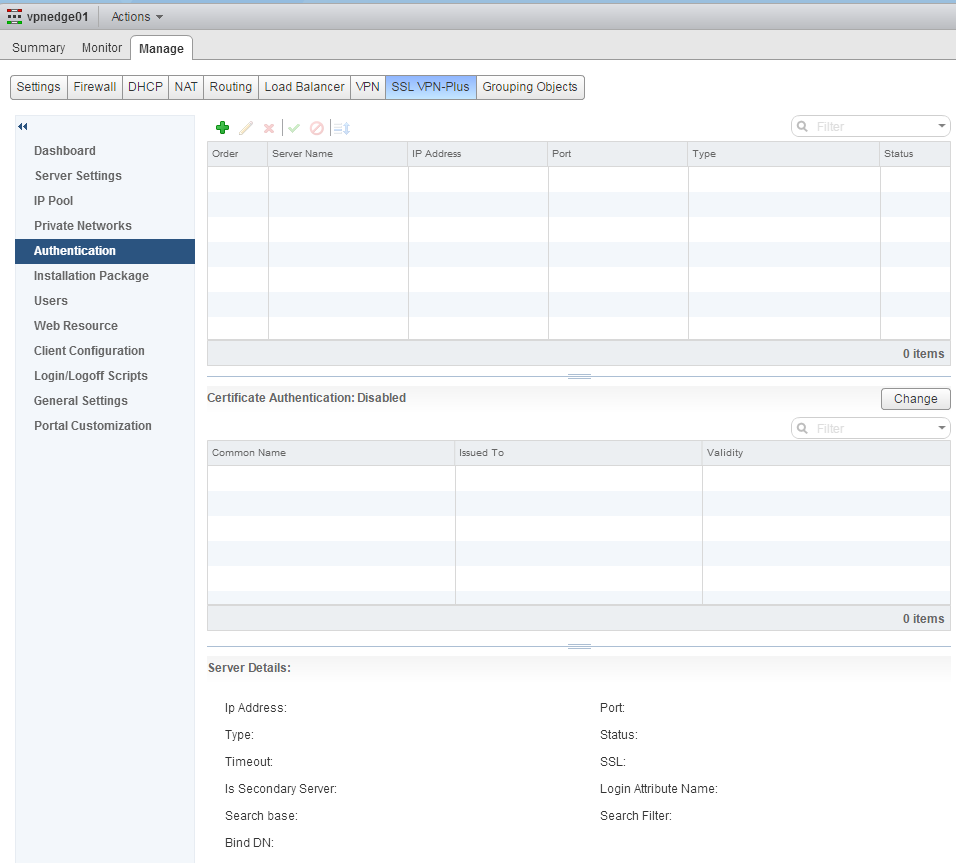
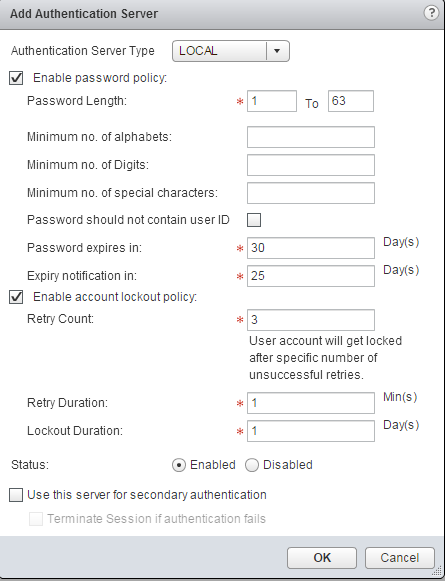
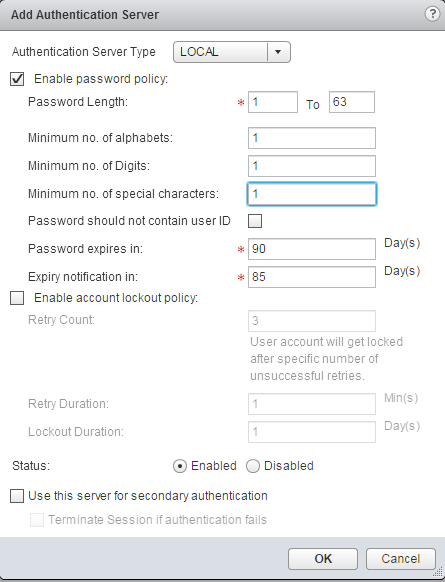
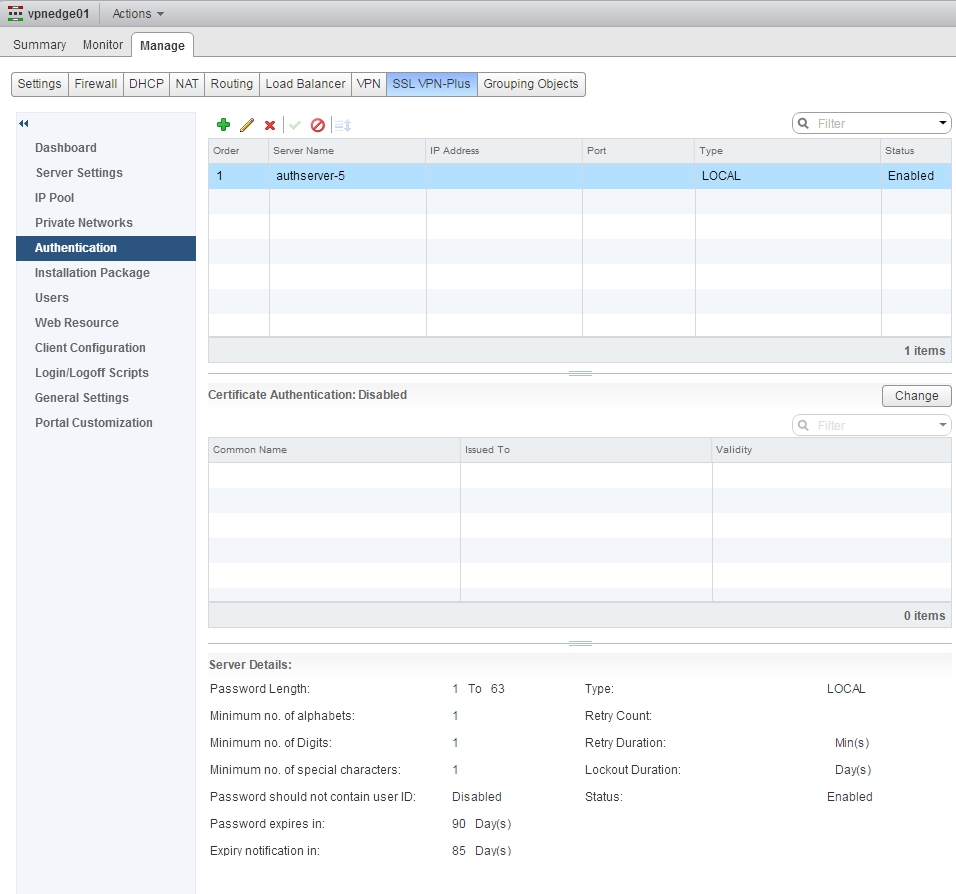
- Select the Authentication tab.
- Select the green plus button to configure an Authentication Server.
- Change the authentication type to LOCAL. Local are user accounts defined in this interface specifically for this NSX Edge Services Gateway.
Configure the desired amounts of rules for user accounts. - Click OK.
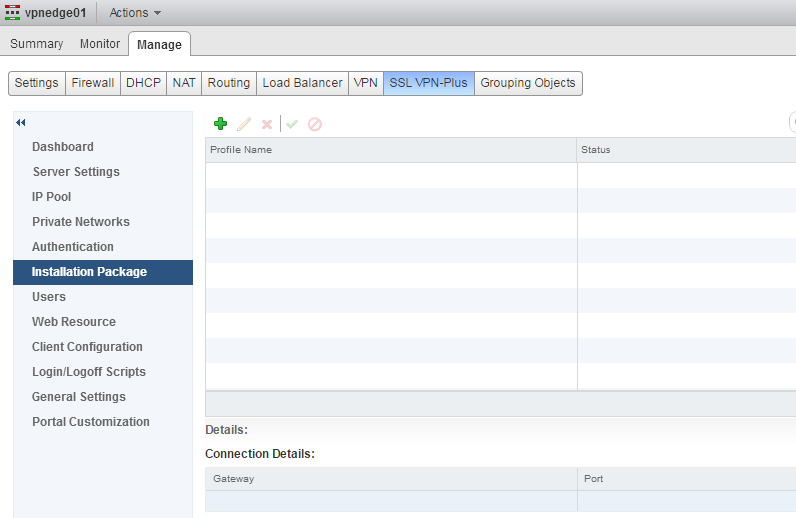
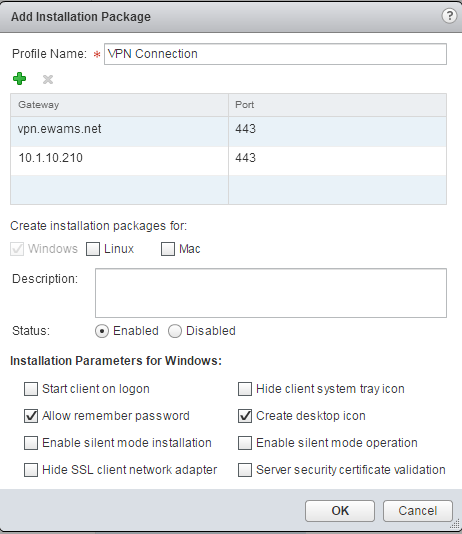
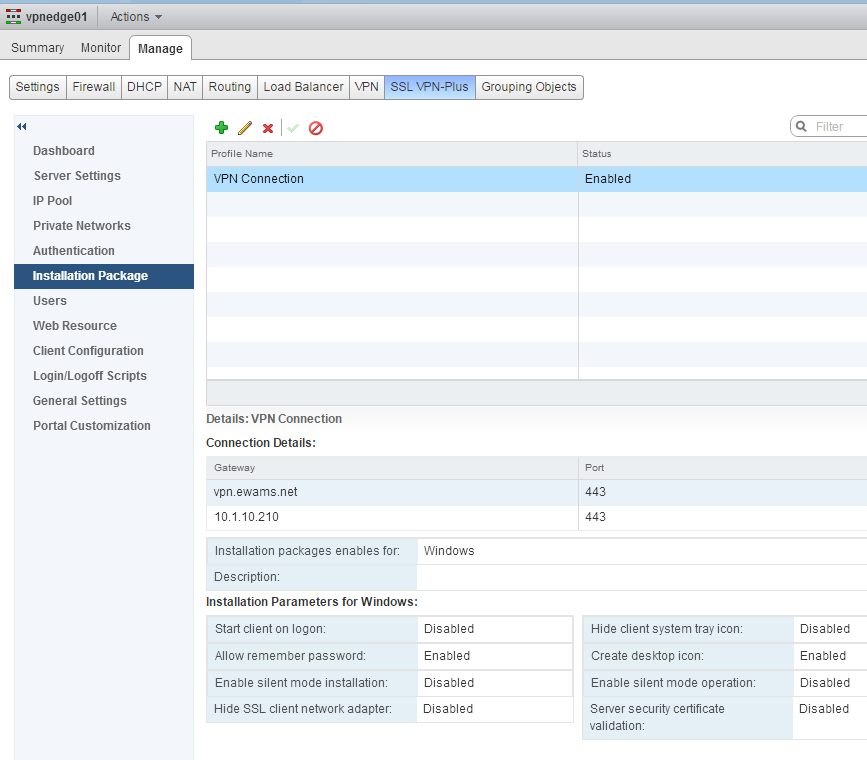
- Select the Installation Package tab.
- Click the green plus button to create an install package.
- Give the Installation Package a name.
Click the green plus button to add a VPN gateway.
Input the name or IP and the port that clients should connect to for a connection to the VPN on the Edge Gateway. If you are using NAT, put the public IP or public DNS entry (such as vpn.ewams.net). Make sure this IP and port is configured to reach the NSX Edge Gateway.
Click OK and add more as needed. (I added my external DNS entry for normal usage and the internal address for testing).
Check the Linux and Mac boxes if you want the system to generate packages for those operating systems.
Provide a description if desired.
Check the boxes for each desired setting. These settings are to configure the actual installation package, for example the box to Enable silent mode means that once the installer is ran it will complete without asking the user anything and then just display the login prompt. - Click OK.
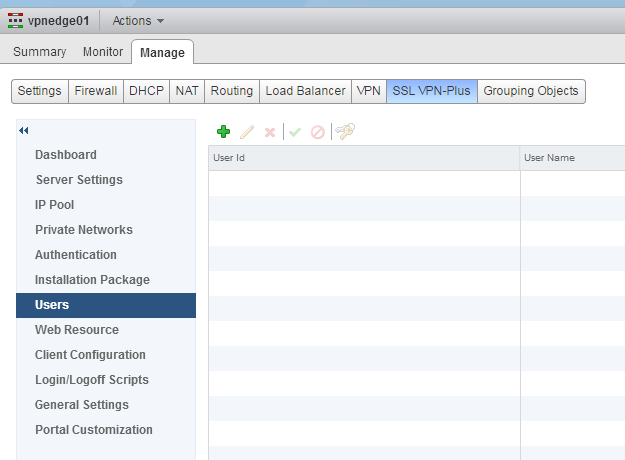
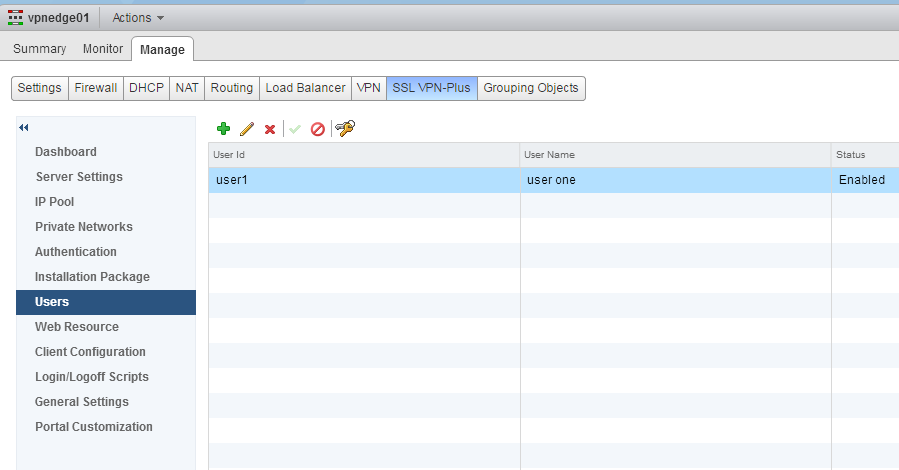
- Click the Users tab.
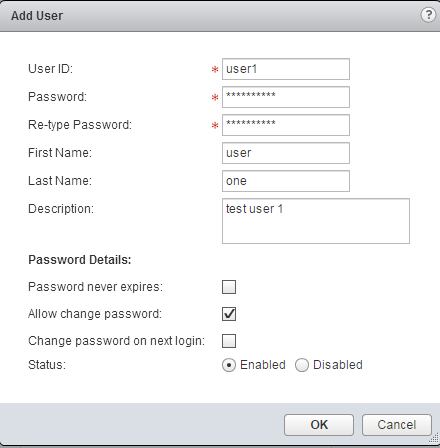
- Click the green plus button to create a VPN user account.
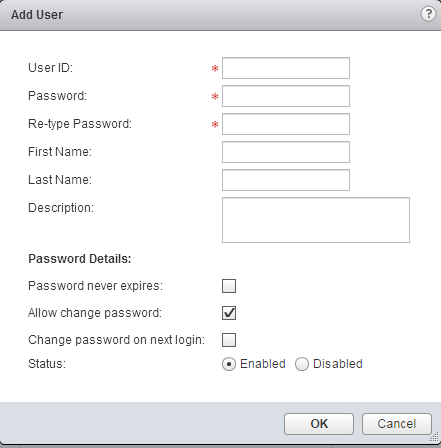
- Input the user ID, this is what the user types when logging in.
Type in the password that matches the security requirements defined in the authentication setup.
Fill in the other name and description tabs as desired.
If you wish for the password to not expire check the box.
If you want to allow the user to change their password through the web interface check the box.
If you want to require the user to change their password when the login the first time check the box.
Leave the account enabled if you want to be able to use it. - Click OK.
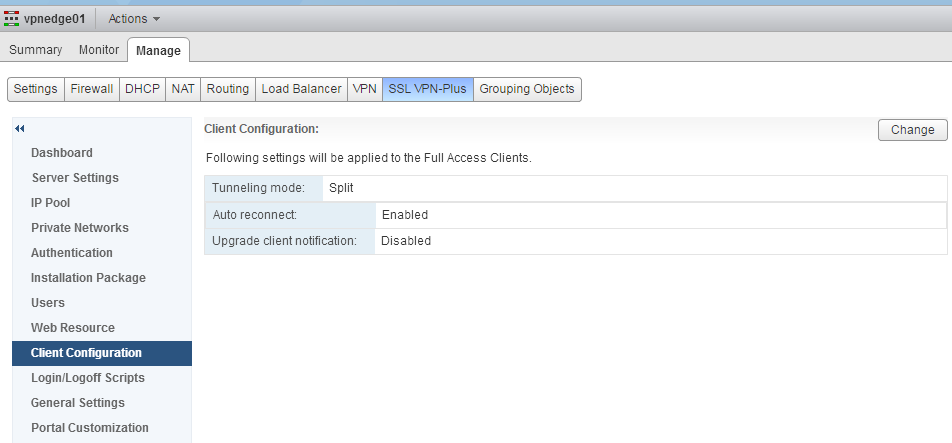
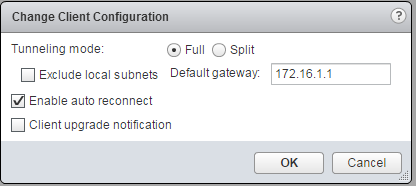
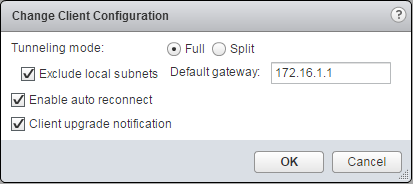
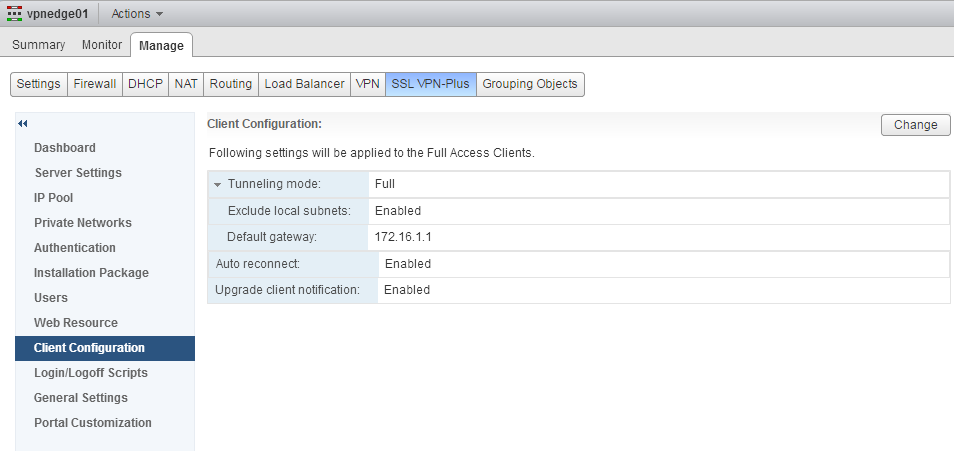
- Click the Client Configuration tab.
- On the top right click the Change button.
- For tunneling mode, "in split tunnel mode, only the VPN flows through the NSX Edge gateway. In full tunnel, the NSX Edge gateway becomes the remote user's default gateway and all traffic (VPN, local, and internet) flows through this gateway."
Check the box to exclude local subnets if you want the VPN to not pass LAN traffic.
Type in the default gateway for the VPN user to be configured with, this should be the gateway you defined in the IP Pool section.
If desired, check the box to enable auto reconnect in the even the client gets disconnected from a poor connection.
Check the box to notify the user when the client has an update. - Click OK.
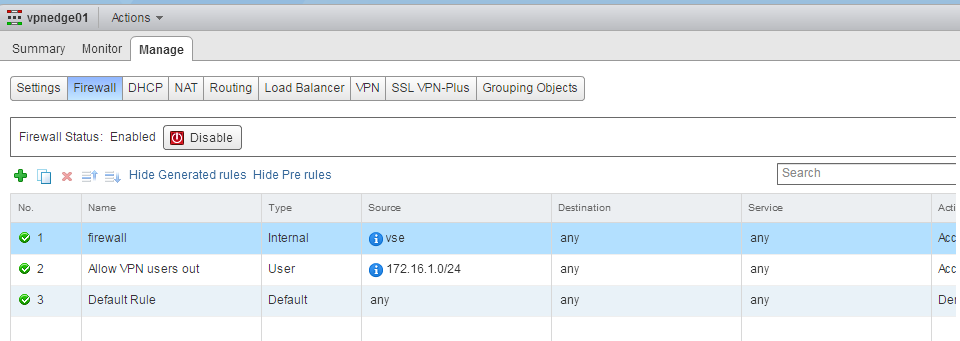
- Click the Firewall tab.
- Create a firewall rule above the default rule that has the source as the IP Pool network or IP Pool range specified above. Set the destination as appropriate. Click publish when done.
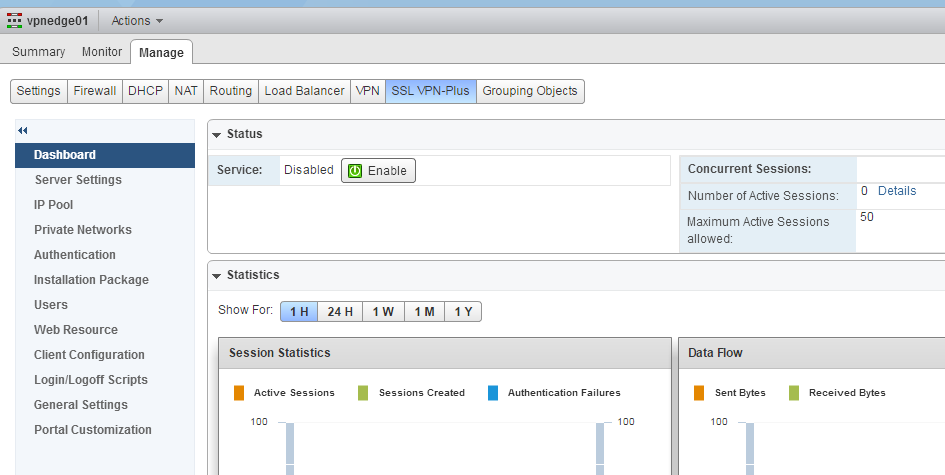
- Go back to the SSL VPN-Plus tab.
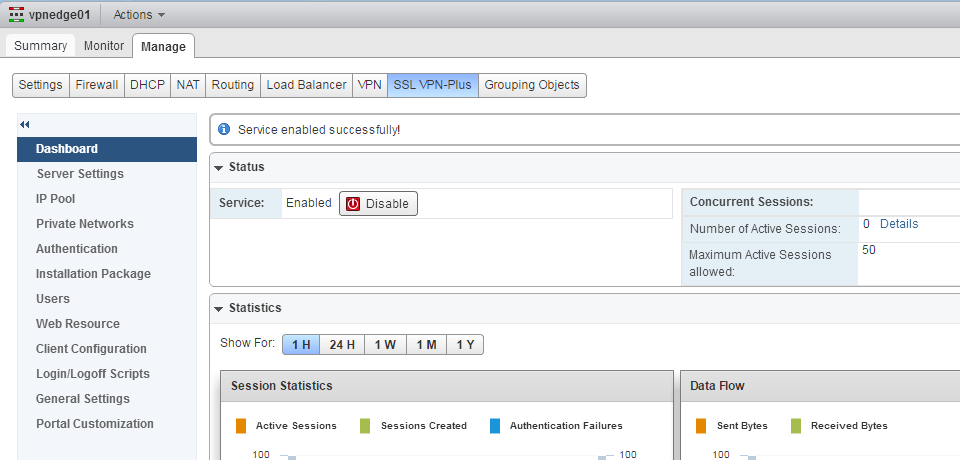
- Select the Dashboard tab.
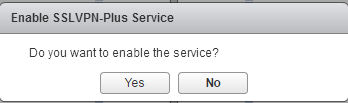
- Under status, click the Enable button.
- Click Yes to enable the service.
- Wait for the service to start and the status to update.
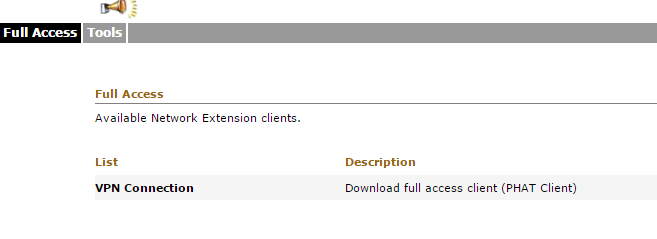
- Open a web browser and go to the URL and port specified.
- Login with the user credentials created.
- Click the name of the client installation package.
- Click the "click here" to start the installation of the SSL VPN Client.
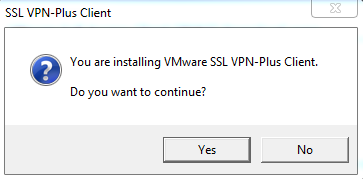
- Perform the install by clicking Yes.
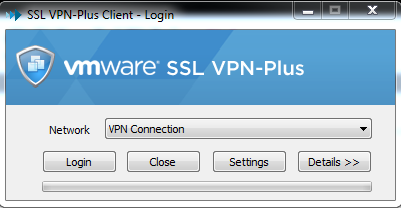
- Click Login.
- Type in the user credentials.
- Allow the connection to initialize.
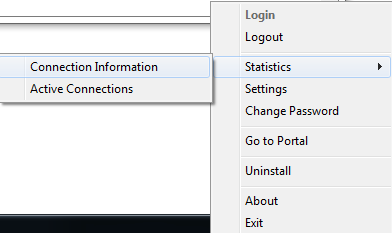
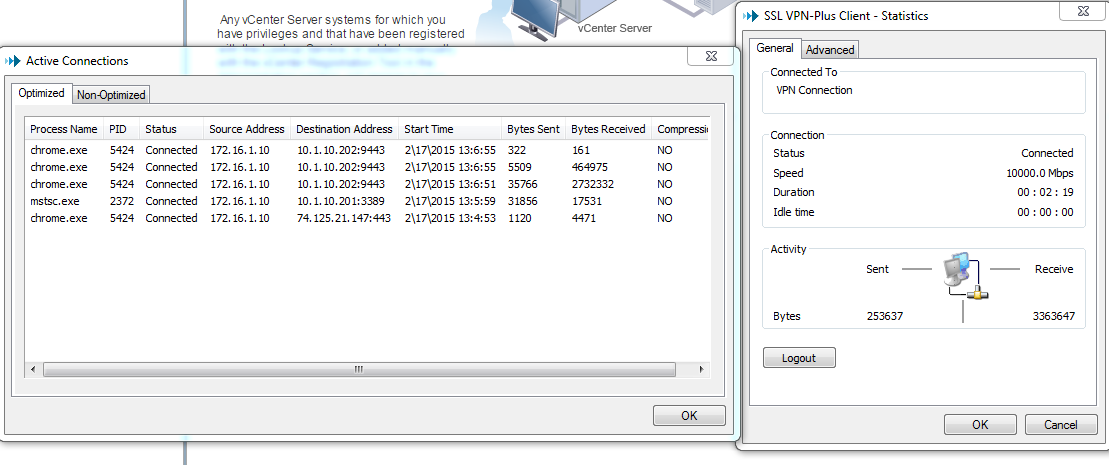
- Right click on the SSL VPN-Plus icon and select Statistics - Active Connections
- Configure more users or different authentication methods.







Conclusion
With this installation guide for VMWare NSX 6.1.2 SSL VPN-Plus you can now provide VPN services using the NSX Edge Services Gateway. The VMware SSL VPN Plus client is simple to use once you have configured the NSX SSL VPN. This guide only showed how to configure local authentication, Active Directory, LDAP and RSA are other options available. I will create a guide on Active Directory SSL VPN authentication in the future and link to it from here.
PS. If anyone from VMware reads this, please notify the NSX team that their documentation is horrible. There is a drastic need for an architecture document or the admin guide to explain what different features and settings do. The install guide is very bare-bones and does not explain what different options do - "Select this or that". And of course all the official and un-official blog posts do not explain anything and just take defaults.
References
- https://www.vmware.com/support/pubs/nsx_pubs.html - NSX Document Repository
- https://pubs.vmware.com/NSX-6/index.jsp?topic=%2Fcom.vmware.nsx.install.doc%2FGUID-311BBB9F-32CC-4633-9F91-26A39296381A.html - NSX System Requirements
Written by Eric Wamsley
Posted: February 17th, 2015 1:40pm
Posted: February 17th, 2015 1:40pm